How To Handle Suspicious Email
There are many reasons to be wary of emails in today's environment that look suspicious in any way. Some email messages may be phishing scams; Some may contain viruses and others malicious software. Files within messages may contain inappropriate images and include web beacons,Which can be used to secretly send the message back to the sender.
If an email looks suspicious, don't put your personal information at risk by opening or replying to the message. Below are some suggested guidelines to help protect yourself from these dangers when suspicious mail arrives in your mailbox:
1. If you receive a phishing e-mail message, do not respond to it. Don't open junk mail at all
First, what is phishing (pronounced "fishing")? It is a type of online identity theft that uses e-mail and fraudulent websites designed to steal your personal data or information such as credit card numbers, passwords, account data or other information. To protect yourself from phishing scams sent via e-mail, don't put your personal information at risk by responding to an email that looks suspicious. Delete junk email messages without opening them. Sometimes even spotting spam can alert the spammer or put an unsecured computer at risk. Do not reply to email unless you are sure the message came from a legitimate source. This includes not responding to messages that offer the option to "remove me from your list". Do not "unsubscribe" unless the mail is from a known or trusted sender. Use junk mail tools in your e-mail program.
2 Approach links in email messages with caution
Links in phishing email messages often take you to fake sites that encourage you to pass on personal or financial information to con artists. Avoid clicking on a link in an email message unless you are sure of the actual target address, URL, or a valid sender.
Most email programs show you the actual target address of a link when you hover over the link in the message.
Before clicking on a link, be sure to read the target address. If the email message appears to be coming from your bank, but the target address is just a meaningless series of numbers, don't click the link.
Make sure the spelling of the words in the link matches your expectation. Spammers and scammers often use URLs with typos and transposed characters that are easy to ignore, such as "Procliam.co.in"
3. Approach images in e-mail with caution.
Just as a beacon within ocean relays a message or data back to a source, images within email messages – also known as "web beacons" – are used to secretly send messages to the sender.
Spammers rely on the information provided by these images to locate active e-mail addresses. Images may also contain harmful codes and can be used to deliver messages to spammers regardless of filter.
The best defense against web beacons is to prevent pictures from being downloaded until you have had a chance to review the message. Most offline mail clients include these settings.
4. Approach attachments in email messages with caution.
Attachments may be viruses or spyware that are downloaded to your machine when you open the attachment file. If you don't know who the attachment belongs to or if you weren't expecting it, don't open the attachment.
5. Don't trust the sender information in an e-mail message.
Even if the email message comes from a particular sender you know and trust, take the same precautions you would use with any other email message. Spoofing is email activity in which the sender's address and other parts of the email header are changed as if the email originated or was sent from another source. This is a common practice by spammers and one of the hardest to combat as there can be legitimate reasons to spoof an address.
6. Don't trust offers that seem too good to be true
If a deal or offer in an email message looks too good to be true, it probably is. The best defense is to exercise your common sense when you read and respond to email messages.
7. Report suspicious email
If you receive a suspicious email that looks like it came from a company that you know and trust, report the email to the faked or "spoofed" organization.
Contact the organization directly (not through the email you received) and ask for confirmation on the validity of the message.
8. Don't enter personal or financial information into pop-up windows
A common phishing technique is to launch a fake pop-up window when someone clicks on a link in phishing. send a message To make the pop-up window more believable, it can be displayed on the window that you Belief. Even if the pop-up window looks official or claims to be secure, avoid entering sensitive information, because there is no way to check the security certificate. Close the pop-up window by clicking The red X in the upper right corner of the "Cancel" button may not work as you would expect.
9. Don't forward chain email messages
Not only do you lose control over who sees your email address making your address susceptible to attacks, but you also may be furthering a fraud or aiding in the delivery of a virus.
10. Update your computer software including OS upgrades, Anti-virus, etc.
How do I report a Phishing or suspicious email?
Reporting suspicious email can reduce the duration and impact of an active phishing attack.
Using the Outlook :
- Open the message
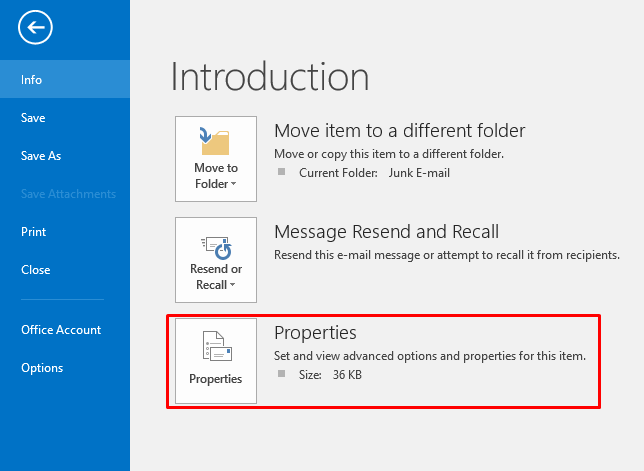
- To the right top corner ,Click File Tab ,click on Properties on Left pane as below.
-
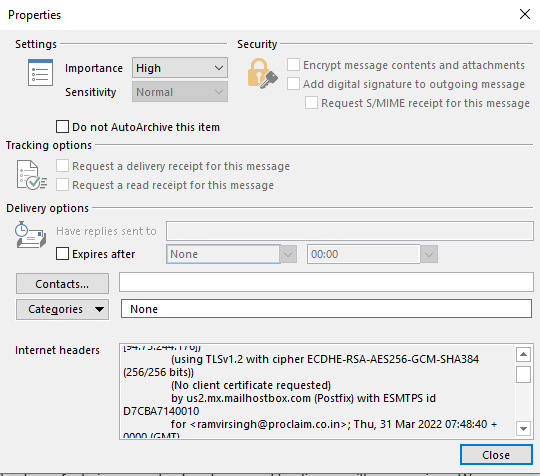
- Copy the Internet Headers as below, and send it at dataprivacy@proclaim.co.in
-